How Can You Tell if an Email Is a Scam?
We’ve all received strange and suspicious emails in our inbox. But while some are easy to identify as spam, others are less obvious.
Maybe it’s an email from Netflix, PayPal, or another account you use, claiming your password’s been compromised. Or an old friend is suddenly reaching out to ask for financial help. These emails look and seem legitimate. But are they?
Hackers use spam emails to “phish” for victims. These legitimate-looking emails are designed to trick you into giving up sensitive information or clicking on malicious links.
And they’re getting more aggressive and sneaky with their scams. The Anti-Phishing Working Group (APWG) reported that nearly 23,000 unique phishing email subject lines were used in September 2022 alone [*].
For unsuspecting victims, scam emails can lead to downloading viruses — or even identity theft and financial fraud. And it’s even worse for businesses. According to the FBI, businesses lost $2.4 billion in 2021 to Business Email Compromise (BEC) scams [*].
Even if you have the tiniest suspicion that an email is from a scammer, stop what you’re doing. Read this guide before you click on a link, respond to a strange email, or download an attachment.
Example: PayPal Scam Email That Looks Real
- It has the service@paypal.com sender label.
- It has a subject line that makes you want to open.
- It has the same font and styling as PayPal.
- It catches you "off-guard" by tricking you into thinking you sent someone money.

How To Identify a Scam Email in 5 Seconds
- Do you personally know the sender?
- Is this an unsolicited email from someone claiming to work for an organization like the FBI or the IRS?
- Is the sender asking for sensitive information like personal details or financial information?
- Is the subject line strange, with unusual punctuation and characters?
- Does the sender’s email address and “from” name match? (You can hover over or click on their name to reveal their email address.)
- Is the sender’s email from a suspicious domain name? (i.e., ebay-support.com)
- Is the email asking you to click on a link, open a cloud storage document (i.e., Google Drive), or download a file?
- Is the sender using urgent or threatening language to get you to act?
- Is the entire email embedded on an image or iframe?
- Are there any grammatical or spelling errors in the email?
- Is the offer in the email too good to be true?
While all of these questions can raise red flags, links and attachments are the biggest warning signs of an email scammer.
Most scam emails you receive will contain a download link or a link to another website. Clicking on them could automatically download a malicious file that infects your computer. Or, it might lead to a legitimate-looking website where you’re asked to provide details such as passwords, credit card numbers, bank login credentials, Social Security numbers (SSN), and more.
These sorts of attacks can happen to anyone.
For example, in early 2020, hackers broke into healthcare insurance provider Magellan’s network by impersonating a client [*].
Once they were in, they stole data and installed malware to steal even more credentials. In the end, they stole the personal information and tax information of 1.7 million victims and sold it on the Dark Web.
Check if your personal data was leaked to hackers in a recent data breach using Aura’s Dark Web Scanner. We’ll scan the Dark Web to see what information or account credentials have been compromised so that you can secure them.
8 Warning Signs of a Scam Email
The above checklist can help you quickly identify if an email is from a scammer. But what if you’re still unsure?
As scammers get more advanced with their attacks, you need to be on the lookout for any sign of a scam email. Here are the key elements that will help you tell if an email is from a scammer:
1. The email comes from a generic domain (Gmail, Yahoo, etc.)
Generic email domains such as @gmail.com, @yahoo.com, @hotmail.com, and @outlook.com are cybercriminals' favorites for sending scam emails.
These accounts are free to use and can be customized to look like they’re coming from a legitimate organization.
A good example is the IRS tax scam [*]. In these scam emails, hackers pretend to be from the IRS and request your SSN to “verify” your identity before they send you a tax refund.
Like most established and reputable organizations, the IRS doesn’t ask for sensitive information via email. And they will never use a generic domain.
Pro tip: Email hackers can “hide” their email addresses to make it look like they’re coming from a legitimate source. Always hover over or click on the “From” name to reveal the sender’s actual email address. If it doesn’t match up with who they say they are, it’s most likely a scam.
Related: Has Your Gmail Been Hacked? Here's How To Secure Your Account →
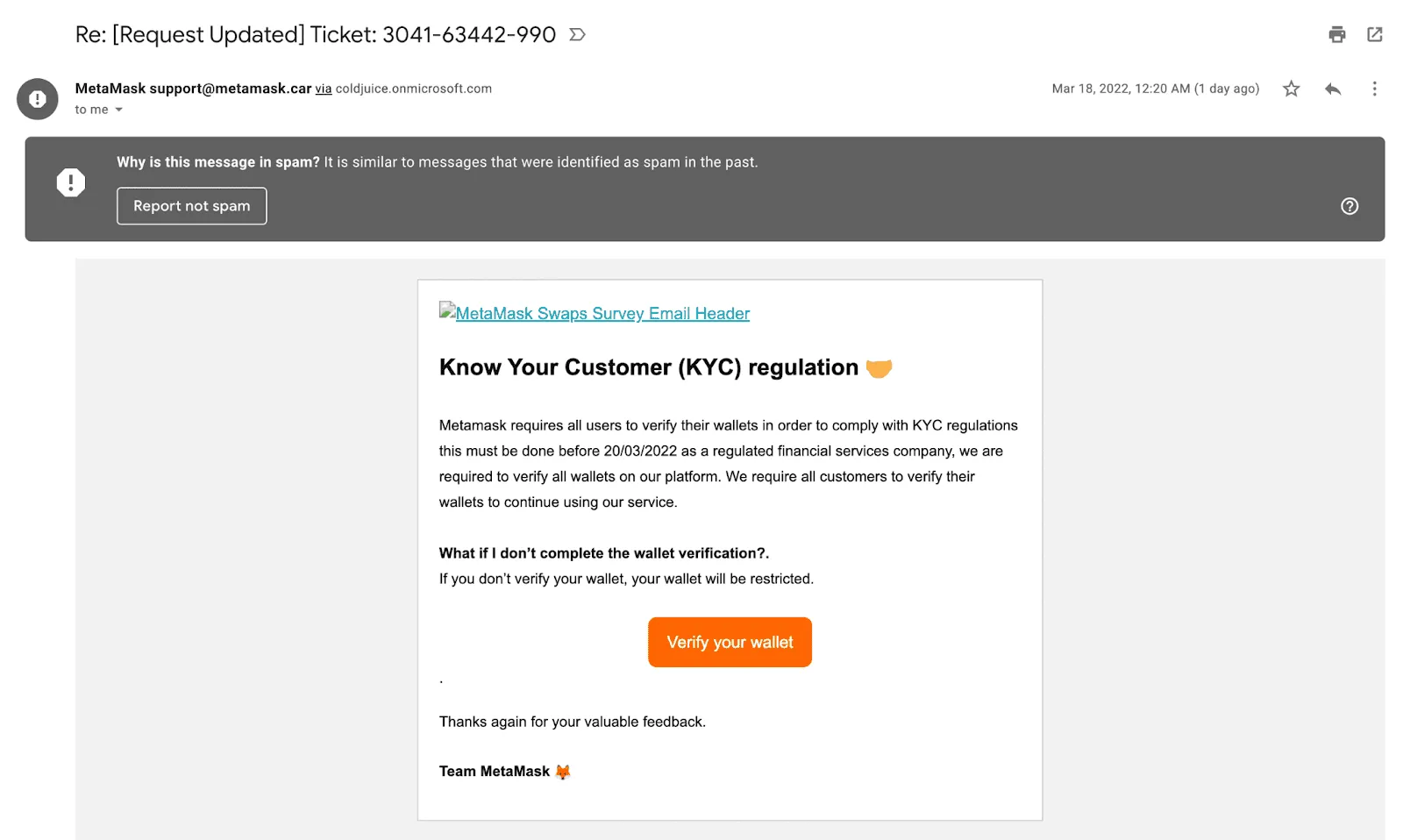
2. Urgent or threatening tone (“Someone has access to your account!”)
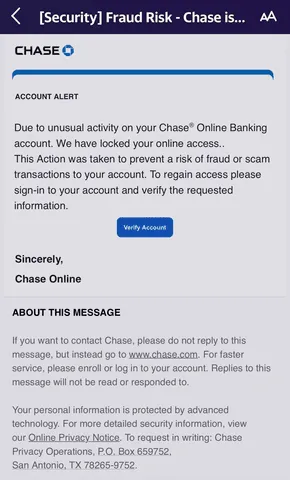
Hackers want you to act quickly without realizing it’s a scam. And the easiest way to do that is to prey on your emotions.
The “scare” tactic is standard in phishing scams. By creating a sense of urgency or fear, they’ll trick you into clicking on a link or downloading a suspicious attachment.
One of the most common phishing messages is claiming that your legitimate accounts have already been hacked. In this scam, they create emails that look like they’re coming from an account you trust and use phrasing such as, “Unauthorized login attempt on your account,” or “We’ve detected some unusual activity.”
The emails will include a link that sends you to a site that prompts you to enter your login credentials in order to ensure your account is safe.
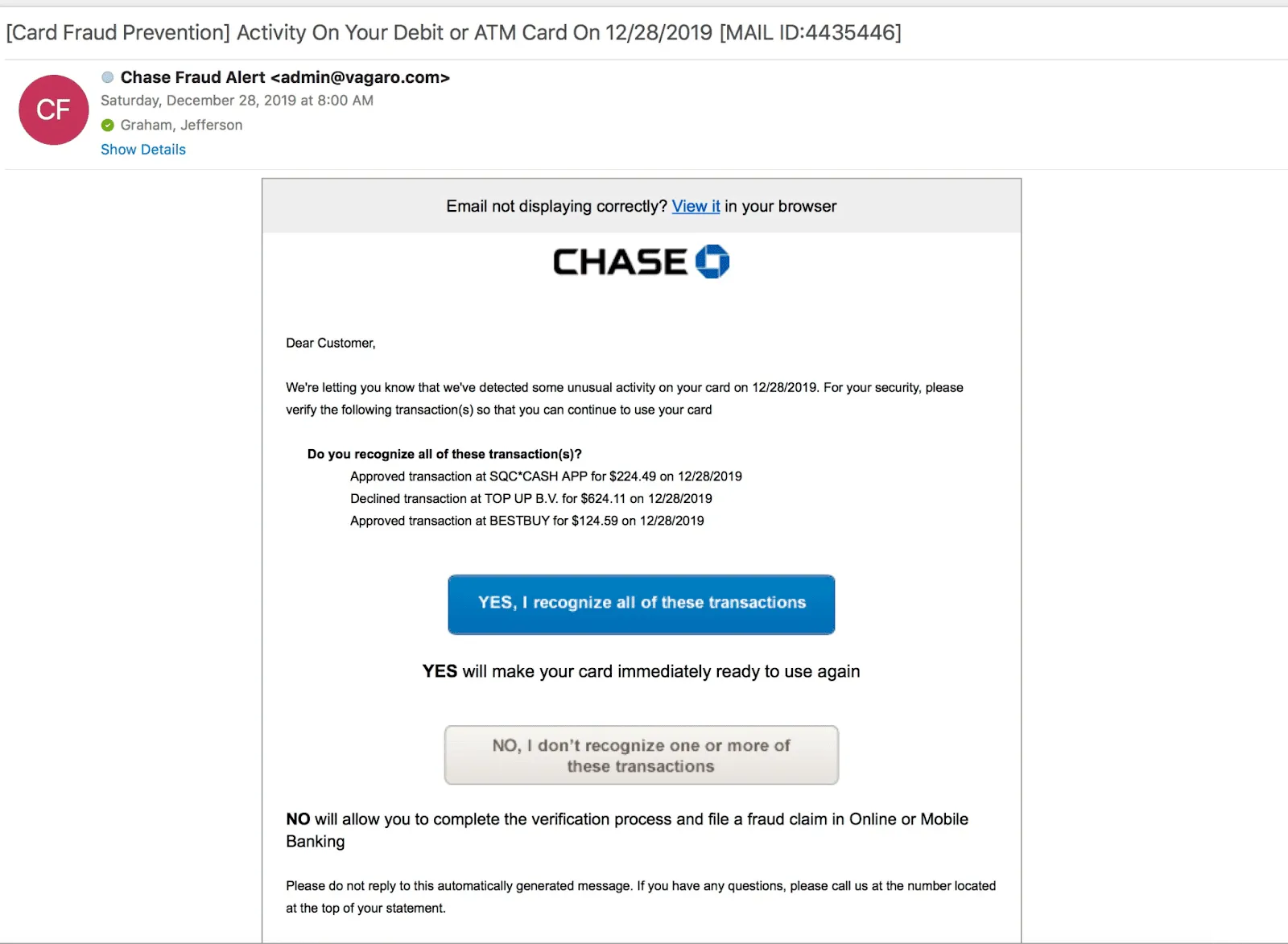
These scam emails can be hard to identify, especially if they reference accounts you actually use.
Before you click on a link, check the “From” email address. Is it from the actual company? If not, it’s a scam.
Pro tip: It’s a good idea to always reach out directly to any company that contacts you unsolicited. Go to their official website and look for a contact form or phone number for customer support. You can ask them to verify that the message is legitimate and not a scam.
Related: The 7 Latest Chase Bank Scams (and How To Avoid Them) →
3. A ‘too good to be true’ promise
Scare tactics aren’t the only way that scammers prey on your emotions. If you receive an email claiming that you qualify for a reward or prize from a contest in which you didn’t participate, it’s likely a scam.
For example, let’s say you’re living in Michigan and you receive an email saying you won a $50,000 prize from a competition in Texas — but you’ve never been to Texas (or entered the contest).
Even if they use your full name or a common username, there’s a pretty low chance that it’s a lucky mistake. Instead, scammers are most likely trying to get you to enter your financial information or download malware on your devices.

These scams can happen over social media, website pop-ups, phone calls, and even text messages. But remember the golden rule of avoiding fraud: If an offer, promise, or opportunity looks “too good to be true,” it almost always is.
Related: Have I Been Hacked? How To Recognize & Recover From a Hack →
4. Missed package delivery scam email
- Has all the classic signs of a scam email.
- Urgency, element of surprise, strange links or QR code.
- Even the footer looks real. They even included privacy policy.
- The strange sender address clearly gives it away.
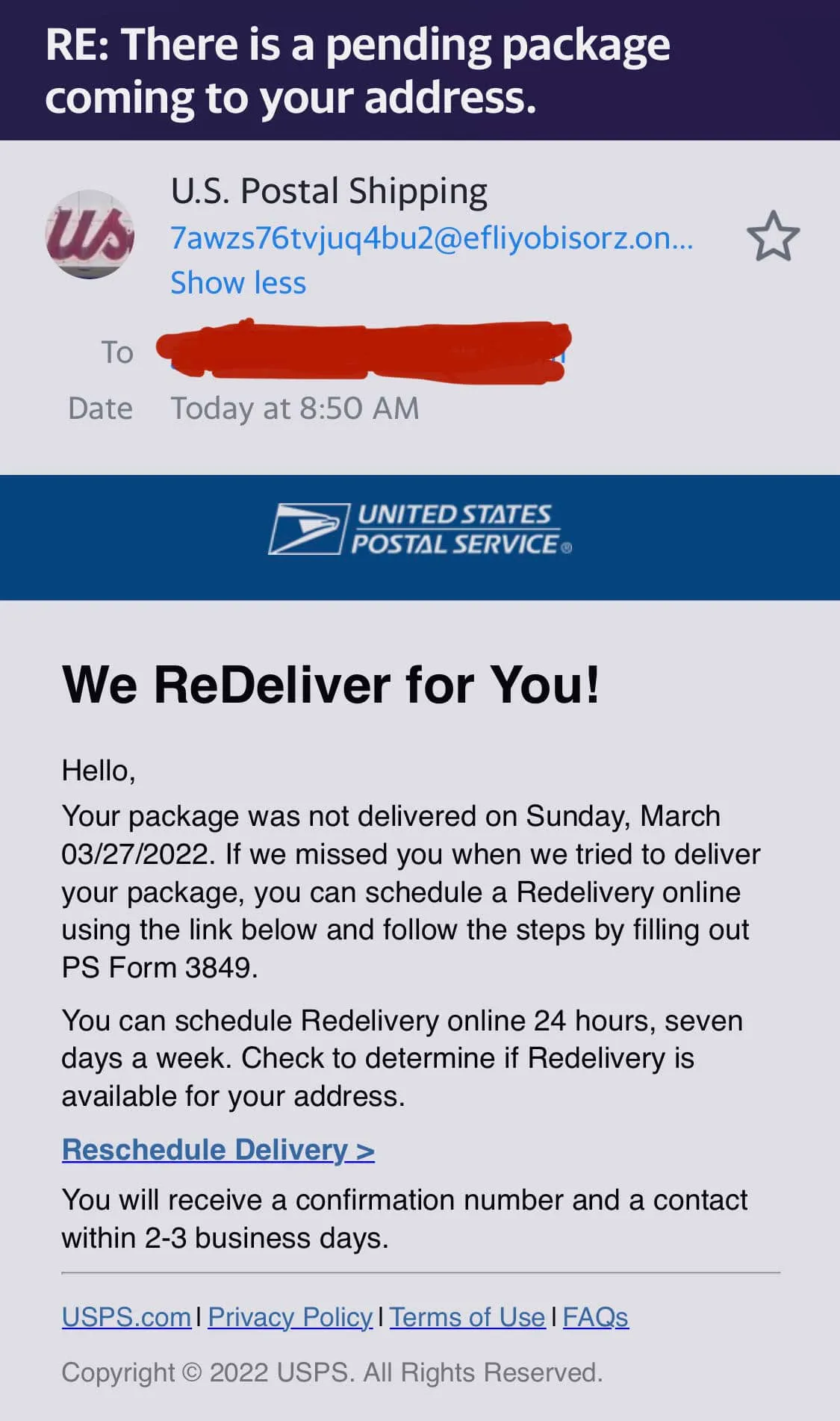
Related: The Latest UPS Fake Delivery Text Message Scams You Need To Know →
5. Suspicious or unexpected links in the body of the email
The goal of most fake emails is for you to click on a link and go to a website that’s designed to steal your sensitive information.
Always double-check email links before clicking on them. You can do this by hovering your cursor over the linked text to see where it takes you. If the link is suspicious or doesn’t match up with what you expect (based on the text or sender’s name), be very cautious.

In one recent example, hackers used this exact tactic to steal more than $650,000 from a San Francisco non-profit organization [*].
Pro tip: Don’t automatically trust links from email addresses you know. Scammers will often hack email addresses or use stolen login credentials purchased from the Dark Web to pretend they’re someone you know or trust. This scam is a type of identity theft called Account Takeovers (ATO).
6. Redirects to unsecure domains (i.e., they’re missing HTTPS)
If you click on a link in a scam email, you’re not automatically at risk.
Most scam email links will send you to a phishing website that asks you to enter sensitive information like your credit card number or account login and password. These sites can look surprisingly real. But there’s one element that almost always gives them away.
Financial institutions and companies handling sensitive information always have HTTPS in their URLs (not HTTP). Sites with HTTPS provide secure communication over a network. For example, your bank uses HTTPS to ensure hackers can’t intercept your account details when you log in.
After clicking any link, check the URL of the site it sends you to. You’ll want to see HTTPS as well as a “lock” icon in your browser’s address bar.
Many scammers will try to trick you by using a URL that looks similar to what you expect to see. For example, they might use “http://www.amaz0n.com” instead of “https://www.amazon.com.”
Or, they might place numbers before the main URL to spoof the main domain. For example, the website shows “http://14f6kl.admin.google.com” instead of “https://www.admin.google.com.” In your hurry, you’ll just see “admin.google.com” and enter your information.
Pro tip: Install antivirus software with malware and phishing protection. Aura protects your devices from viruses and will alert you of potential phishing sites.
7. Poor grammar and spelling errors
We all make spelling and grammar mistakes from time to time. But hackers have a reputation for sending strangely-worded or formatted scam emails.
If an email doesn’t read properly — especially if it claims to be from a large organization — that’s a huge red flag that you’re dealing with a scammer.
Unfortunately, these errors can sometimes go unnoticed as we quickly scan through our inbox.
Look at the text in the email below. At first glance, you won't pick up the grammatical errors.
But on a second pass, you’ll start to see typos and unusual grammar, such as the sentence structure.
.webp)
Poor spelling and grammar don’t automatically mean you’re looking at a scam email. But it’s a warning sign that you should be careful about taking any further action.
8. Strange attachments (even trustworthy ones like Google Docs)
Malicious attachments in emails are among the most common phishing attacks from scammers.
By downloading an attachment, you might accidentally install malware on your device that hackers can use to spy on you, steal your sensitive information including bank account numbers and passwords, or even lock your device (i.e., ransomware).
Hackers often disguise these viruses as legitimate files, such as invoices or software updates. These emails will even use your real information — name, email address, and more (all stolen from the Dark Web).
.webp)
Another scam is to “hide” malware inside services you know and trust like Google Docs or Microsoft Word. This is called a trojan (after the famous wooden horse).
Once you click on the download link, there’s a high probability you’re downloading malware that is capable of infecting your computer.
Recent scams to be aware of: Hackers are now taking this scam up a notch by calling you before sending the scam email. On the call, they may pose as your bank and claim “there was an unsuccessful login attempt on your account.”
As a result, they’ll send you an email containing an attachment requesting that you change your login credentials. Once you receive this email and download the attachment, you give the hackers access to your information.
Related: How to Stop Spam Emails (2023 Guide) →
What Happens if You Open a Scam Email?
Here’s the good news: Scammers can’t do much if all you do is open a scam email.
However, you’re putting your personal and financial information at risk if you:
- Click on a phishing link.
- Download a malicious email attachment.
- Respond with sensitive information (like your bank login credentials or credit card details).
So, does this mean you’re completely safe if you only open scam emails (but don’t click on any links)? Not exactly.
If your email provider is set to automatically load images, then hackers can actually learn a lot about you, including:
- Your location.
- The internet service provider or mobile carrier you use.
- The device you used to open the email (desktop, tablet, iPhone / Android).
- What operating system you’re using (iOS, Mac, Android, Microsoft Windows, Linux).
- The email client you’re using (Apple Mail, Outlook, Gmail, or Yahoo Mail).
- Which web browser you’re using (Apple Safari, Google Chrome, or Firefox).
That’s a lot of information hackers can use for future, more sophisticated social engineering attacks.
Pro tip: Turn off automatic image loading in your email provider. Most services will let you change this in your email account settings.
Did You Click on a Link in a Scam Email?
Mistakes happen. And hackers are adept at tricking you into clicking on links in scam emails.
If you clicked a link or downloaded an attachment, don’t panic. Instead, follow these steps:
- Disconnect from your Wi-Fi or mobile network. If you’re on your mobile device and using either a mobile network or Wi-Fi, turn it off immediately. And if you’re on a desktop, turn off the Wi-Fi function. The probability of malware sending data from your devices without an internet connection is low.
- Scan your device for malware or viruses. Scammers have ways of manipulating malware and viruses to lay dormant until they need them. A good way of detecting and getting rid of them is by using antivirus software.
- Change your passwords immediately. Your old passwords become ineffective when hackers breach your data. With malware, they can crack the username and passwords to any of your online accounts. An excellent way to lock them out is to log in to your account and change your passwords.
- Secure your accounts. Changing your password sets hackers back a few weeks or months until they can re-access your account. However, enabling 2FA (two-factor authentication) and setting up a password manager provides better security for your account.

- Check your email security settings. If hackers get into your inbox, they can gain access to most of your other accounts. Make sure you’ve enabled two-factor authentication for your primary inbox and have an active backup account ready to go.
- Report the scam. If you receive a phishing email, forward it to the Anti-Phishing Working Group at reportphishing@apwg.org. And if it’s a phishing attack, report to the FTC at https://reportfraud.ftc.gov/.
- Back up your sensitive files. A good rule of thumb is to keep copies of all your files in cases of data breach or loss. Back up sensitive information like photos, documents, videos, and other important files to an external drive.
- Scan the Dark Web for your information. Having your information circulating on the Dark Web constantly opens you up to receiving attacks from hackers. For example, the leaking of sensitive information such as your SSN allows hackers the chance to steal your identity.
- Consider signing up for an identity theft protection service. Aura protects your sensitive accounts, devices, and networks from hackers and scammers. Plus, if the worst happens, you’re covered by a $1,000,000 insurance policy for eligible losses due to identity theft.
Related: Phishing Email Examples: 20 Emails That Don’t Look Like It →
How To Protect Yourself From Email Scammers and Hackers
Scam emails aren’t going away. If anything, you’re only going to get more of them in the future.
While spam filters are getting better at keeping your inbox safe, 96% of phishing attacks still arrive by email [*], amounting to over $323 million in losses [*].
Here are five ways you can keep your email accounts, identity, and money safe from scammers and cybersecurity threats:
- Don’t reply to spam messages. If you see an email from someone you don’t know or anything about the email looks hasty, delete it. Responding to an email shows the scammer your address is active and increases the chances of getting similar scam emails.
- Never ignore software updates. Scammers take advantage of outdated software and operating systems to install malware and other viruses. Regularly keep your software up-to-date to avoid exposing your data to cyber threats like zero-day vulnerability attacks.
- Install antivirus and phishing protection software. Manually filtering each of your emails for scams is difficult, time-consuming, and doesn’t guarantee 100% protection. Installing an antivirus and phishing protection software will help filter and secure all your emails by quarantining any malicious content.
- Don’t click on links or download any attachments. If you suspect the authenticity of an email, don’t click on links or download any attachments. Instead, verify the contact's identity by calling or researching the source. Sometimes, scammers will provide their contact details in an email. Don’t use them. Instead, do your research.
- Be cautious in revealing personal information. Suddenly receiving an email from someone claiming to be your longtime friend is a social engineering tactic hackers use to trick you into revealing personal information. Once you receive this kind of email, don’t reply or give out your personal details — even your name.
You use your email for everything, from keeping in touch with friends to getting your monthly bills. And that makes it a prime target for hackers and scammers.
Follow these tips to keep your accounts safe. And for added protection, consider signing up for Aura’s identity theft and device protection service.



.svg)


